Resolution
In this article we will assume that you are using Windows and Windows DNS to implement DKIM. Some of this article will also apply to other platforms.
1. https://indy.fulgan.com/SSL/ - Download the latest Windows OpenSSL binaries.
2. Create a folder called C:\OpenSSL-win64 and extract the content downloaded from step 1.
3. In the folder create a new batch file with the contents below. I have called mine DKIM.bat.
@echo off
IF EXIST rsa.private.%1 GOTO exists
C:\openssl-win64\openssl genrsa -out rsa.private.%1 1024
C:\openssl-win64\openssl rsa -in rsa.private.%1 -out rsa.public.%1 -pubout -outform PEM
echo Files created for %1
GOTO done
:exists
ECHO Files for %1 not created because they already exist.
ECHO Please, erase them or try a different name.
ECHO .
:done
4. Open a CMD and change the directory to the OpenSSL location we created earlier.
CD c:\openssl-win64
5. Run the following command
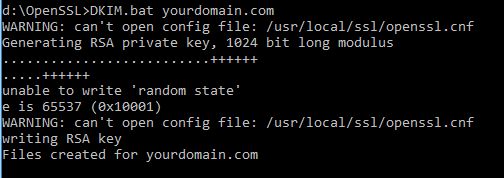
DKIM.bat YOURDOMAINHERE.COM
The result will look similar to the below.
NOTE - You can ignore the warnings
6. This will create two files in your C:\openssl-win64 folder. These are your public and private keys and will be used to sign your emails.

7. Open the rsa.publicyourdomain.com file in notepad and copy the contents.

8. Open the DNS Manager console on your EXTERNAL facing DNS server. We need to create two records. one will tell mail servers we use DKIM and to eit
9. Open the correct zone and Right Click and select Other New Record. From the window that appears click Text (TXT).

10. Enter values below.
Record Name - _domainkey
Text (Value) - o=~
Note - The value above may be changed later. The ~ denotes a soft fail. - means hard fail.

11. Repeat step 9 then enter the values below, using the text copied from step 7.
Record Name - dkim._domainkey
Text (Value) - v=DKIM1; k=rsa; t=y; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQCrLMi7h6oN0uJ7GBNNmuqBqi6+
rrIMVAozyc7Mb9GNAFq+4Bww1GPd04MLjRu6wXVesqBpAGVvcCIOJIC5YNo3yyv2
Pncd9Xa3PcoxGQyGq0xxzUixuMHNZCMArYcqOddiuSvWqyXoKxbBY+TjfKNwOnqb
KuXaJoQoPFg43PKX0QIDAQAB

Here is a quick explanation of what the values in the record above mean
v=DKIM1 - Informs the lookup that the DKIM version used is version 1.
k= RSA - Not strictly needed but tells lookup which type of encryption is used.
t=Y - This tells the lookup/mail server that Testing is On, and will not reject messages. We will remove this later, once testing is complete.
p= - This is the public key data that will be used to decrypt the private key that signed the email.
13. The next step will depend very much on how and what you have configured in terms of email security. Many will simply have an email appliance and will need to enter the private key and selector. In my case i tested on a Sophos UTM appliance.
For the Sophos UTM go to Email Protection > SMTP > Advanced and enter the the details for your domain.

12. Now the DNS records are in place, this can take some time to propagate around the worlds DNS, possibly up to 24 hours depending on your TTL.
To test if all is well we will use two methods. Firstly MXtoolbox provides a great lookup tool.
https://mxtoolbox.com/dkim.aspx
Then we will also send an email to an FREE online service that tests the records and emails you a report.
check-auth@verifier.port25.com
If the config is NOT correct or incomplete (DNS Record missing) you will receive an email an email like the below.

If the config is CORRECT you will receive an email like the below.

13. Once the get a DKIM Pass you can go back to the record in step 11 and remove the t=y; to fully activate DKIM.
So there you have it, not that difficult to do :) hit me up in the comments if you are having problems.


No comments:
Post a Comment